The Attacks Won’t Stop. It’s Time PNG Businesses Did Something About It.
By Steve Percy Superfast IT Networks No CommentsMost cyberattacks are not sophisticated. They don’t need to be.
Attackers use automated tools that scan every corner of the internet, around the clock, looking for one thing: an easy way in. A weak password. An unpatched system. An employee who clicks the wrong link. Find one, and they’re inside your business—often before anyone notices.
The businesses that survive cyberattacks—and increasingly in PNG, businesses are surviving them, or not—aren’t necessarily the ones with the biggest IT departments. They’re the ones that fixed the basics before the attack came.
This is your practical starting point.
Understand What Attackers Are Actually Looking For
Before you can defend your business, you need to think like the threat. Attackers aren’t looking to challenge themselves. They’re looking for the path of least resistance. And across the Asia-Pacific region—which now attracts more cyberattacks than anywhere else on earth—that path runs through businesses that have never properly locked the doors.
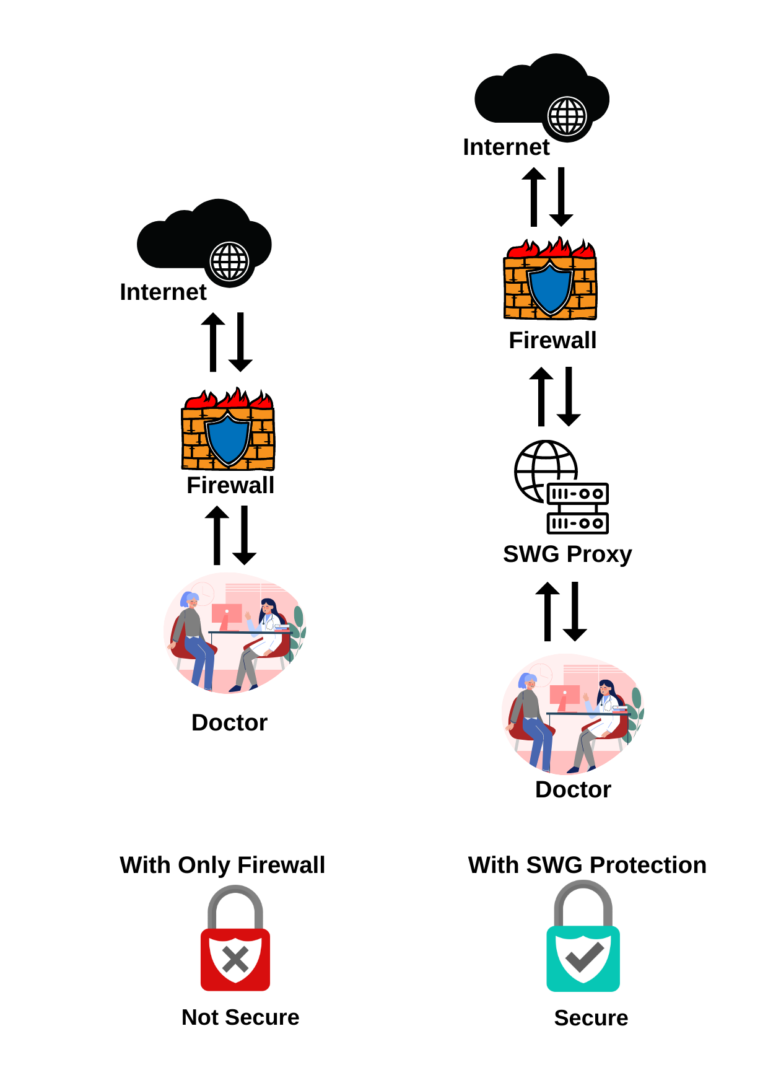
The entry points are almost always the same: stolen or guessable credentials, software that hasn’t been updated in months, staff who haven’t been trained to recognise a phishing email, and systems with no monitoring in place. Fix these, and you eliminate the vast majority of your risk.
The Five Controls That Actually Matter
Security frameworks can run to hundreds of controls. For most PNG businesses, these five will do more to reduce real-world risk than anything else.
MFA requires users to verify their identity beyond just a password—typically a code sent to their phone or an app confirmation. It is the single most effective technical control available. Microsoft’s data shows MFA blocks over 99% of automated account compromise attacks. Turn it on for email, banking, cloud storage, and any remote access to your network. Do it this week.
When software vendors release security patches, they are also publishing a map of the vulnerabilities they’ve just fixed—and attackers read that map. Unpatched systems are a primary entry point for compromise across the region. Set a monthly schedule. Prioritise anything internet-facing. In PNG, where bandwidth constraints make large updates inconvenient, schedule patches during off-peak hours—but don’t skip them.
Ransomware is one of the most destructive threats facing PNG businesses—but its power is almost entirely dependent on your having no clean copy of your data to restore from. Apply the 3-2-1 rule: three copies of your data, on two different media, with one stored offsite or in secure cloud storage. Critically—test your restoration process every quarter. Backups that have never been tested are not backups.
Phishing—emails, messages, or links designed to trick staff into handing over credentials or installing malware—remains the number one entry point for attacks globally. AI is now making phishing messages harder to spot than ever. In PNG’s mobile-first, WhatsApp-and-Facebook business culture, these attacks don’t only arrive via email—they come through every channel your team uses.
Thirty minutes of practical security training every quarter—what to look for, what to do when something seems wrong, who to call—changes your risk profile significantly. The cost is minimal. The impact is not.
When an attack happens—and for a growing number of PNG businesses, it will—the organisations that recover fastest are the ones that knew what to do before the crisis hit. Your plan doesn’t need to be complex. It needs to answer four questions: Who do we call first? Who has authority to take systems offline? How do we communicate with staff and customers? What are our legal and regulatory obligations?
Write the answers down. Share them with your leadership team. Review them annually. That’s it.
Why PNG Businesses Face a Higher Bar
Every business faces cyber risk. PNG businesses face additional headwinds that make the basics harder to get right.
Intermittent connectivity creates patching gaps and makes cloud-based security tools less reliable. A shallow local talent pool means expert help is hard to find quickly when something goes wrong. And PNG’s rapid digital growth is outpacing security investment—a gap that both criminal and state-sponsored actors are actively exploiting across the Pacific.
This context doesn’t change what needs to be done. It changes how urgently it needs to happen—and how much it matters to work with a partner who understands the local environment, not just global frameworks.
The Regulatory Landscape Is Shifting
PNG’s National Cyber Security Strategy sets a clear direction of travel. Businesses that handle customer data, financial records, or government contracts will face increasing pressure to demonstrate minimum security standards. This isn’t a distant prospect—it’s already shaping procurement decisions and partner requirements across the region.
The businesses building these foundations now are making a strategic investment. When compliance requirements tighten, they won’t be starting from zero.
Cybersecurity is not a technology problem. It’s a business decision. And in PNG in 2025, it’s one that can no longer be deferred.
Ready to Take Action? Sprint Networks is hosting SecurePNG—a practical, hands-on cybersecurity workshop built specifically for PNG business owners and IT managers.
You’ll walk away with a clear picture of where your business is exposed and a prioritised plan to fix it. Register for the SecurePNG Workshop → Seats are limited.
Don’t wait for an incident to force your hand.