SASE, the VPN 2.0
Traditional VPN’s allow two IP enabled devices to communicate with each other through a secure tunnel remotely over the Internet, just as if the devices were connected on the same physical local network. VPN’s were originally designed to allow few employees within a company to work remotely. However, as a result of a global pandemic, majority of the businesses were forced to allow employees to work remotely, thus putting a massive strain on traditional VPN’s. Although traditional VPN is widely used and suits the general purpose of interconnecting remote networks quite well, it has some serious drawbacks for security, monitoring, management of end points and not built with the massive adoption of cloud applications in mind.
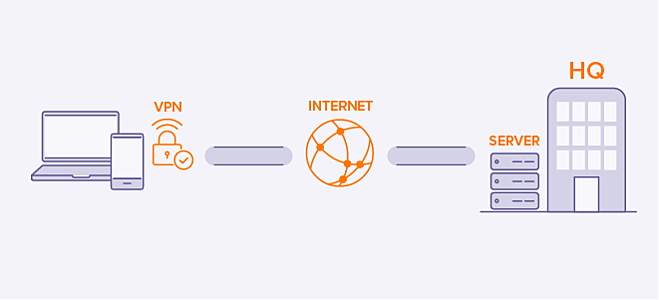
Figure 1 – Traditional VPN Setup
From a technology management perspective, VPNs are highly demanding. They require configuration, deployment, troubleshooting, monitoring, and decommissioning of each user. As VPNs are the gatekeepers of the entire corporate network, they require constant attention. And a number of additional systems are needed to support a VPN to deliver daily connectivity, onboarding, offboarding, and general monitoring. Furthermore, these legacy solutions rely on aging and cumbersome hardware and software, and as a result, can be quite difficult to integrate with the many other components of an enterprise’s technology and security stack. The continuous bandwidth required to keep VPNs afloat is not only costly, but also often taps senior IT resources, distracting them from more proactive, impactful, and innovative business imperatives.
From a technology management perspective, VPNs are highly demanding. They require configuration, deployment, troubleshooting, monitoring, and decommissioning of each user. As VPNs are the gatekeepers of the entire corporate network, they require constant attention. And a number of additional systems are needed to support a VPN to deliver daily connectivity, onboarding, offboarding, and general monitoring. Furthermore, these legacy solutions rely on aging and cumbersome hardware and software, and as a result, can be quite difficult to integrate with the many other components of an enterprise’s technology and security stack. The continuous bandwidth required to keep VPNs afloat is not only costly, but also often taps senior IT resources, distracting them from more proactive, impactful, and innovative business imperatives.
SASE (Secure Access Service Edge) is a simpler and safer access solution that companies can embrace to take advantage of the true power of the cloud. SASE enables IT personnel to closly monitor all inbound firewall ports, and can combine intelligence into decision making — looking at users, devices, and locations, as well as patterns of access, which up levels security. As SASE is cloud-based, it doesn’t need to backhaul internet traffic through data centers. Instead, SASE sends traffic through globally distributed “PoPs” (Points of Presence). The PoP inspects and then sends traffic over the internet or SASE architecture to its destination.
For example, suppose an employee is VPNing into his corporate network from his Sydney home, and the data center happens to be in Melbourne. Ordinarily the traffic would all be directed to Melbourne data center. However, if he’s accessing internet content, it would be optimal to egress that traffic directly out of the device in Sydney, SASE enables this. Only when the user wants to access resources in the Melbourne office will his traffic be backhauled to the data center. All internet traffic will exit directly out of the nearest POP while maintaining the same level of security seen at the data center.
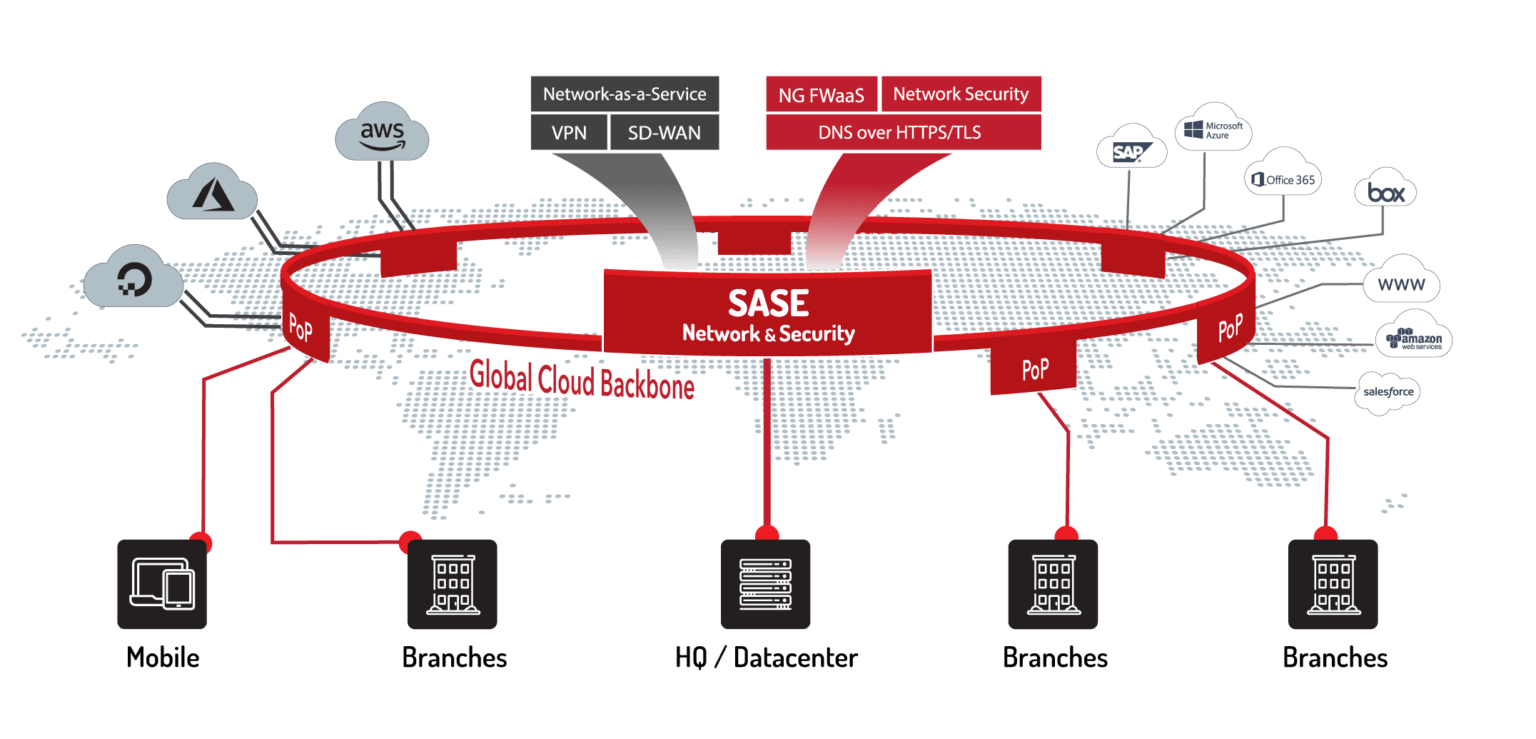
Figure 1 – SASE Setup
As shown in the image above SASE is a global cloud backbone which has multiple functions built right in such as Network Security, DNS filtering, Firewall as a Service (FWaaS), Data Loss Prevention (DLP). SASE is not just another VPN, its so much more. The beauty in SASE is a set of capabilities that you can adopt or introduce at your own pace. Adopting services that are right for your business, your budget and your use-cases. Some SASE capabilities, such as Secure Access or Zero Trust, are a set of security controls that follow the user. Whether they are at home or in the office. SASE puts you in control to adopt at your own speed, whether you need to sweat VPN assets or provide more business centric security and rigour to support good posture for internal or external compliance/regulatory standards.